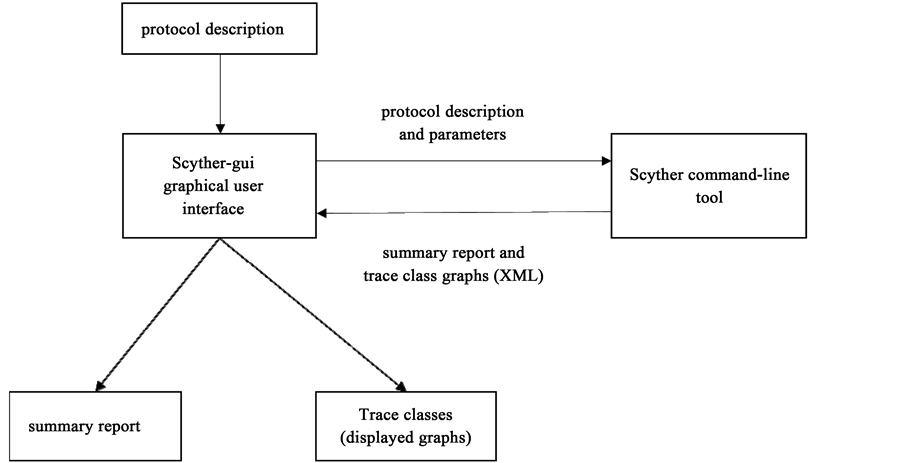
![PDF] The Scyther Tool: Verification, Falsification, and Analysis of Security Protocols | Semantic Scholar PDF] The Scyther Tool: Verification, Falsification, and Analysis of Security Protocols | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/3e8a202085b8b28e914db02ccc22201dc77dc968/2-Figure1-1.png)
PDF] The Scyther Tool: Verification, Falsification, and Analysis of Security Protocols | Semantic Scholar
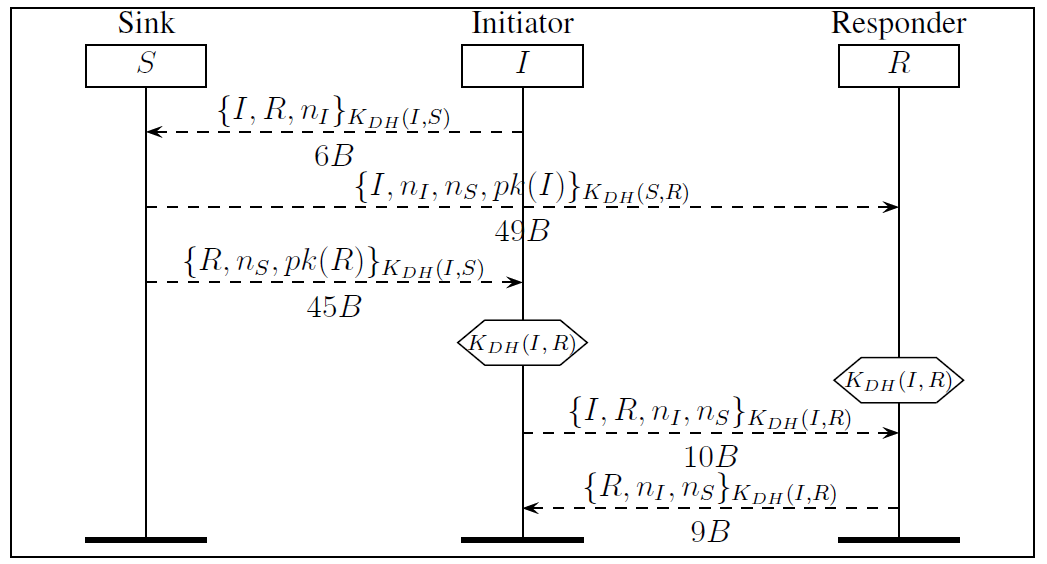
JSAN | Free Full-Text | Evaluation of Secure Multi-Hop Node Authentication and Key Establishment Mechanisms for Wireless Sensor Networks | HTML
Assessment of Threats to the Security of the Cryptographic Authentication Mechanisms of the Monitor Devices of Vehicles | KnE Engineering

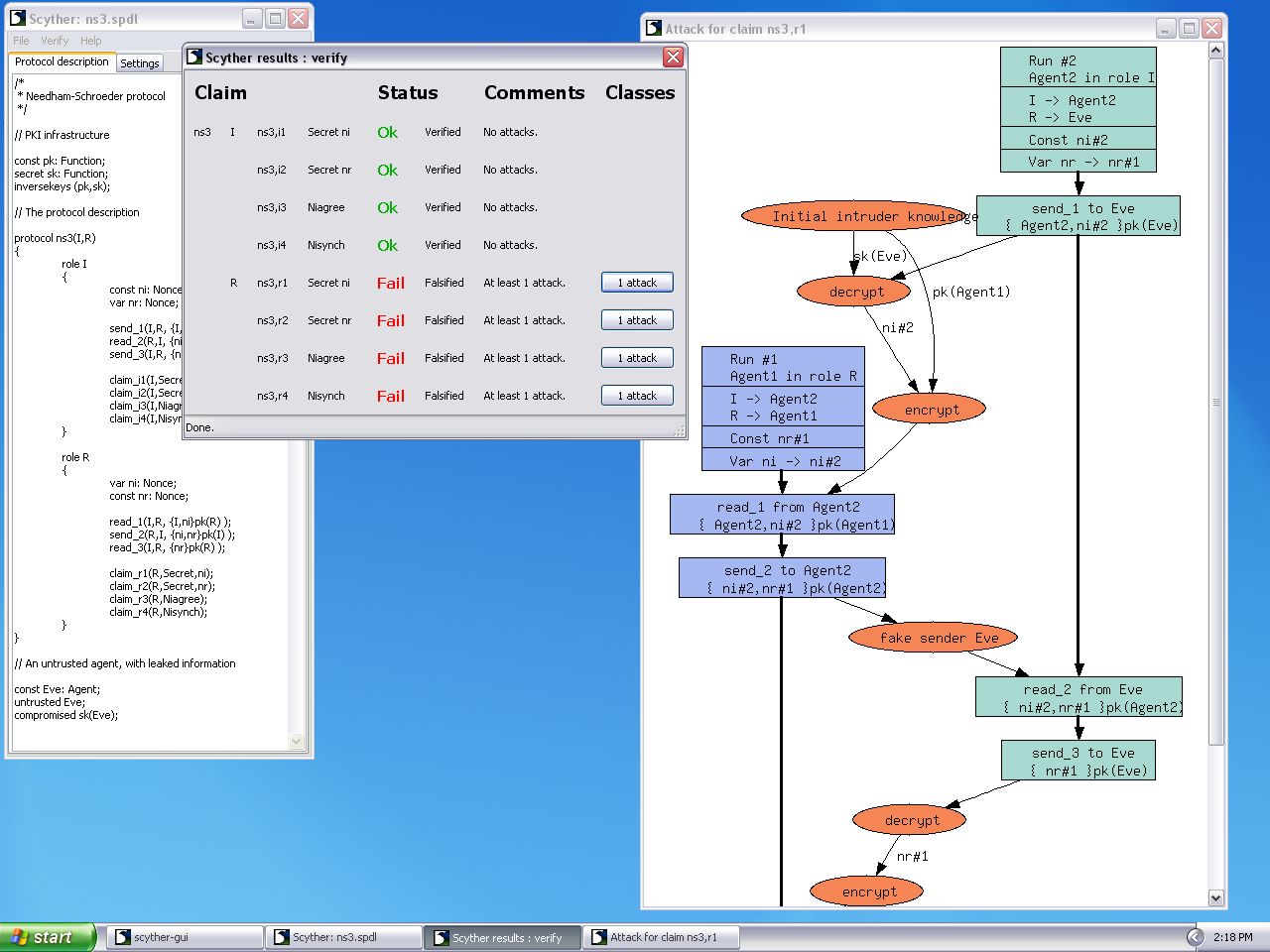
The results using 'verification claim' procedure in Scyther tool (see... | Download Scientific Diagram

Scyther (Formal Verification Tool) Installation on Windows #Scyther #Formalverification #Windows - YouTube
GitHub - meiersi/scyther-proof: A tool for the automatic generation of Isabelle/HOL correctness proofs for security protocols.
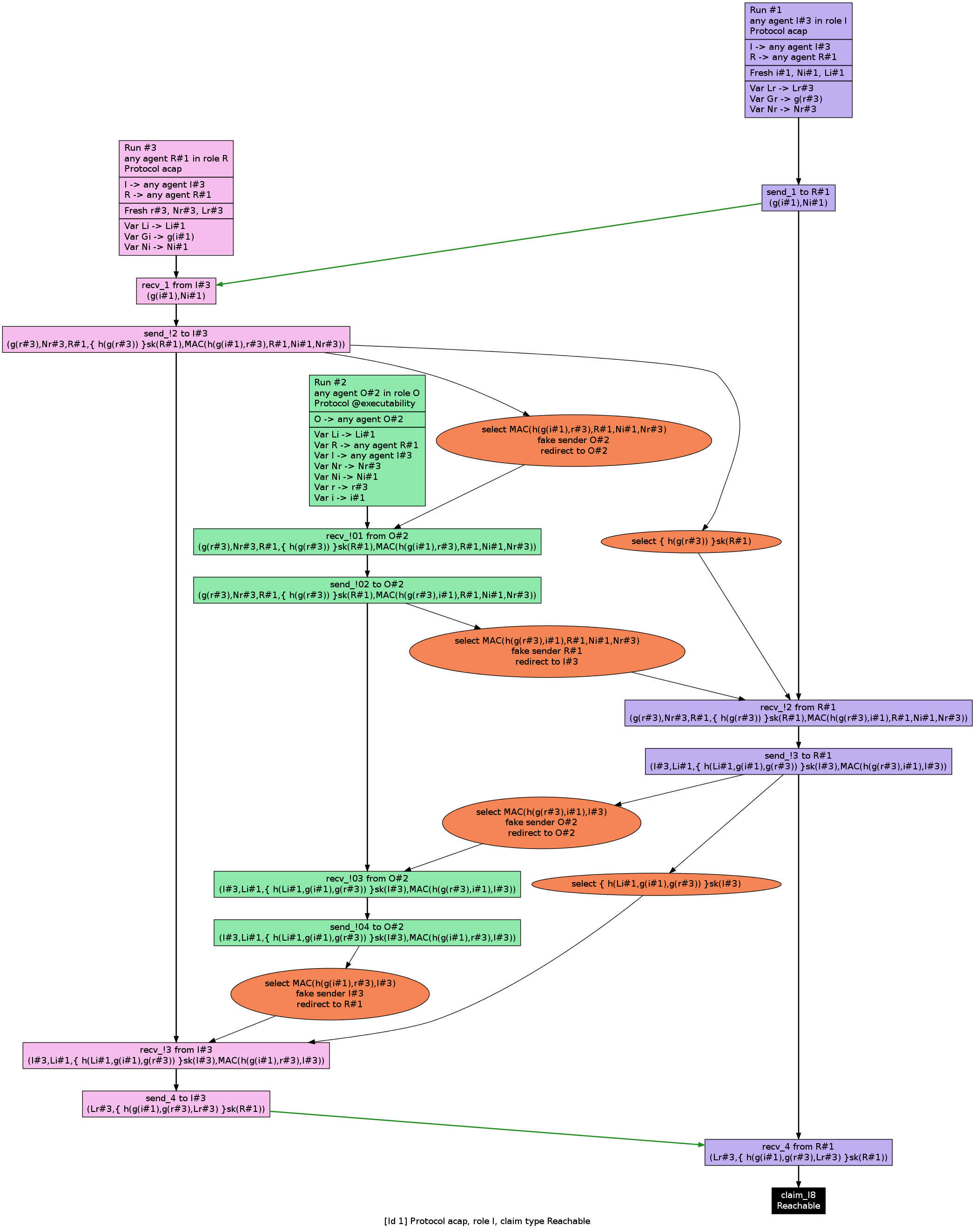
![PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/df932f9db948e0e49c26a748ca2eec9d76e3c118/6-Figure4-1.png)
PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar

scyther tool installation on windows. Scyther model checker installation on windows OS. Formal Verif - YouTube